Strada Security
9/23/2025
Strada is a secure peer-to-peer platform that brings modern cloud SaaS security models to the edge. Our goal is to enable seamless and secure access to a customer’s media from anywhere in the world — without moving any data into centralized cloud storage.
Security Philosophy
Strada was designed around a simple security principle: data should remain under the owner’s control at all times.
Traditional cloud storage products require customers to centralize media in large multi-tenant environments. While seemingly convenient, this architecture creates a large concentration of valuable data that must be protected and continuously monitored.
Strada takes a different approach: instead of moving media into a cloud storage product, Strada enables secure peer-to-peer access directly to a customer’s infrastructure and hardware. Media remains on the systems a customer controls — whether an editor’s workstation, a facility server, or on-premises storage.
This architecture dramatically reduces the amount of sensitive data stored within Strada’s own cloud infrastructure and limits the potential impact of any centralized compromise.
Strada’s cloud infrastructure & services focus on authentication, authorization, coordination, and secure connectivity, while the actual media remains under the customer’s direct control.
Key Security Components
Authentication
Almost all modern security practices start with user authentication as a foundational element. Strada’s authentication system leverages the world’s largest third-party identity management platform, Auth0, as its identity provider. This allows customers to choose from various login methods in order to authenticate the Strada application:
Sign in with Google
Sign in with Apple (only available on iOS)
Sign in with email and unique password
When using what is known as ‘social sign-in’ (Google or Apple), a customer’s Strada account is locked behind the iron-clad protocols that have been developed to keep data safe. Workspace administrators of those platforms can enforce any of the login standards (2FA, SSO, Passkey, etc…) they support. Auth0 and Strada have no workarounds to these enforcements; they are controlled completely through those social sign-in providers.
When using email and unique password, Strada is still locked behind an end-to-end encrypted authentication flow. Credentials used for email/password authentication are processed and stored by Auth0 and are not accessible by Strada or its employees. At this time, however, the traditional email/password login process does not support 2FA, SSO, or Passkey login.
Recommendation: Enforce Strada access through Google Workspace authentication for centralized identity management. This is the easiest and most secure way to manage Strada access.
Strada Agents
The Strada Agent software is a desktop application that customers download (MacOS and Windows support is available today, with Linux on the roadmap). Once downloaded and authenticated with the same protocols described above, the Agent serves as the main access point for remote collaborators to access media on the customer’s computer. If the Strada Agent application is logged out or offline, no remote access sessions can be established.
In fact, Strada has a large advantage over all cloud storage products, because customers are able to completely unplug or remove drives from their computers. In those cases, no remote collaborator can access the customer’s media without requesting that the drive be physically plugged back in. In other words, Strada enables cloud-like access while allowing customers to completely air-gap media by simply disconnecting the drive.
Strada does not store any media or cache any media in our cloud infrastructure under any circumstance; all the data lives on the customer’s hardware. Whether that data is in a facility or on an editor’s desk, customers can trust they control their data at all times.
Peer-to-Peer Security Model
Strada uses a peer-to-peer networking architecture that allows authenticated customers to securely connect directly to Strada Agents.
All peer connections are authenticated using public-key cryptography and encrypted using modern transport encryption. These keys are generated locally on the device and are never shared with Strada infrastructure, ensuring that only authorized peers can establish connections.
This model eliminates the need to route media through centralized cloud storage infrastructure. Instead, Strada coordinates secure connections between authenticated devices, allowing data to travel directly between trusted endpoints.
Because media is transferred directly between peers:
Media is never stored in Strada’s cloud infrastructure
Media is never cached in Strada systems
Media remains entirely within the infrastructure controlled by the customer
This architecture significantly reduces centralized data risk while still providing the accessibility and collaboration features customers typically associate with cloud products.
Authorization
Strada follows a best-in-class authorization technique known as Role Based Access Control (RBAC). Once a Customer or Strada Software Agent is authenticated to Strada, that does not grant them access to anything — it simply tells us who they are. Once identity is established, our RBAC system determines which resources the customer is authorized to access.
At the core of RBAC are three main terms
Objects — this is the resource or entity the Subject is attempting to access or update. It can be a file, an agent, another customer, a job, an invite — every distinguishable resource or entity is its own object type and has its own role based access controls.
Subjects — this is the actor of an Action. The Subject is typically a customer, but it also can be an internal Strada service. Not even Strada’s internal systems can access a customer’s resources without first being explicitly granted permission to do so. This is a best in class practice known as Zero Trust, which Strada is constantly striving to maintain.
Action — the action a Subject is trying to take, including delete an agent, invite a customer, start a transfer, etc.
Every API request is authorized through our RBAC security system. If a customer’s access is revoked, they immediately, without delay, lose all access to the objects they previously had access to. If a customer’s role is changed, the actions they can take are immediately updated to reflect their new role. While this is standard in cloud products, Strada has brought this technology to the edge to work on a customer’s hardware, which enables a new era and standard of security.
Features
Strada includes several features designed to provide practical security controls for organizations managing sensitive media.
Folder-based access controls. Strada allows for granular access to media, granting access down to the folder level — no matter how deep in a directory. If a customer wants a remote collaborator to have access to a single directory, they can do just that. If a customer wants an Administrator to see everything, they can do that as well. Folder access is instant for adding, updating, and removing remote collaborators.
Public Link. On any public link that a customer wants to share, they can set an optional password or expiration date. These settings are changeable at any time by the customer. The link can also be deleted by the customer or Administrator at any time and is reflected instantly.
Delete Account. We believe customers own their data, which is why we enable them to completely delete their Strada accounts. In traditional cloud products, this is challenging because deleting an account is at odds with security; this often creates a trade-off between data ownership and recoverability. We know customers want control over their data — which means the ability to completely remove it — but that opens the door for it to be completely removed without any recovery mechanism should there be a mistake. With Strada, because all of a customer’s media is always in their possession, deleting a Strada account never deletes any media. We delete any invites, links, and anonymize any data that is associated with the account.
Infrastructure Security
Strada hosts its core services on Amazon Web Services (AWS) and operates with a layered infrastructure security model designed to minimize attack surface, enforce strong access controls, and maintain continuous visibility into our environment.
All production infrastructure runs inside an AWS Virtual Private Cloud (VPC). Compute instances operate within private subnets, meaning they are not directly accessible from the public internet.
External traffic enters the system through AWS Load Balancers, which route requests through Strada’s Identity & Access Proxy before reaching internal services. This architecture ensures that authentication and access validation occurs before any request is allowed to reach our application services.
Access between internal services is tightly controlled using AWS Security Groups and Kubernetes network policies. These controls ensure that services can only communicate with the specific systems required for their operation, preventing unnecessary lateral movement within the infrastructure.
Our containerized workloads are isolated using Kubernetes namespaces, further segmenting services and enforcing minimal communication paths between workloads.
Strada’s underlying compute hosts run Bottlerocket as their operating system. Bottlerocket is purpose-built for container environments and is designed around three core principles: minimal footprint, safe automated updates, and a security-first architecture. By removing unnecessary packages and services, Bottlerocket significantly reduces the attack surface of the underlying infrastructure.
Infrastructure Patching
Strada follows an infrastructure maintenance philosophy of operating within N-1 of the latest supported platform versions, where N represents the most current release. This approach allows us to adopt modern security improvements while maintaining stable and predictable production environments.
This philosophy extends across our core infrastructure platforms, including Bottlerocket host operating systems and Amazon EKS Kubernetes clusters. Staying within N-1 ensures we benefit from the latest security hardening, performance improvements, and platform reliability updates without introducing unnecessary operational risk.
If a critical security vulnerability is identified, Strada accelerates patching immediately based on AWS Security Bulletins and other relevant security advisories.
Data Security
Strada intentionally stores minimal metadata related to workspaces, customers, and agents (as a reminder, Strada does not store or process customer media files within our cloud infrastructure). This metadata is encrypted at rest using AES-256 encryption, and all data in transit is protected using TLS encryption.
Peer-to-peer communication between Strada Agents uses Ed25519 cryptographic keys, ensuring secure authentication and encrypted communication between participating devices.
Production databases are never exposed to the public internet. They operate exclusively within Strada’s private AWS network and communicate with other infrastructure components using internal VPC networking.
Administrative access to production databases is tightly controlled and requires access through a secured bastion host. The bastion host itself is accessible only through Strada’s internal Zero Trust network, adding additional layers of protection before any database access is possible.
Access to sensitive metadata follows the principle of least privilege. Only a limited number of engineers have read-only access for operational purposes, and elevated permissions are tightly restricted and audited.
Security Review
Strada has successfully completed the AWS Foundational Technical Review (FTR), which evaluates solutions against AWS architectural best practices for security, reliability, and operational excellence.
To continuously monitor the health and security posture of our cloud environment, we leverage services such as AWS Config and AWS Security Hub. These tools help identify configuration drift, detect potential misconfigurations, and ensure our infrastructure remains aligned with AWS security best practices.
Strada is actively progressing toward SOC 2 Type II and ISO 27001 certifications as part of our broader security and compliance roadmap.
These efforts reflect our commitment to implementing security controls, operational processes, and audit practices that meet internationally-recognized standards.
In addition to external certification efforts, Strada conducts internal security reviews of infrastructure configuration, access policies, and system architecture on a recurring basis. These reviews help ensure our security controls continue to evolve alongside the platform as it grows.
Internal Security Posture
Internal Zero Trust Network
Strada operates with a Zero Trust internal network model. Access to internal systems, infrastructure, and production resources requires authenticated network access through this secured environment.
If a device disconnects from the network or loses authentication, access to internal systems is immediately revoked.
AWS Account Security
Access to Strada’s AWS infrastructure requires multi-factor authentication (MFA) and follows AWS best practices for identity and permission management.
We enforce least-privilege access policies, ensuring employees only have access to the resources necessary to perform their roles.
Password policies align with current NIST guidance, and we enforce credential hygiene practices such as access key rotation.
Internal access permissions are reviewed every 90 days to ensure roles remain appropriately scoped.
Employee On-boarding and Off-boarding
Employee onboarding follows the principle of least privilege, ensuring individuals receive access only to the systems required to perform their role.
Access provisioning is performed by the Security Engineer and reviewed by the Head of Engineering.
When an employee leaves Strada, access revocation begins immediately. Network access is disabled first, preventing further access to internal systems or infrastructure.
Off-boarding procedures are executed by the Security Engineer and verified by the Head of Engineering to ensure all access has been fully removed.
Comparison to Traditional Cloud Storage
Traditional cloud storage products require media to be uploaded into centralized cloud environments before it can be accessed or shared. This model introduces several security considerations:
Media is stored in shared multi-tenant infrastructure
Large datasets are replicated across multiple cloud systems
Access control mistakes can expose entire storage buckets
Centralized breaches can expose large amounts of customer data
Strada avoids many of these risks by keeping media outside of centralized cloud infrastructure.
Instead of uploading media to a shared cloud environment, Strada enables secure access directly to a customer’s infrastructure. Media stays on the hardware and storage systems the customer already trusts and controls. This allows customers to maintain full ownership over their media while still benefiting from modern collaboration features such as remote access, role-based permissions, and secure sharing.
In practice, this means Strada delivers the convenience of cloud collaboration while maintaining the security posture of local infrastructure.
While Strada’s architecture minimizes centralized data storage, we maintain strong security controls across the cloud infrastructure that powers authentication, authorization, and system coordination.
Security is an ongoing process at Strada, and we continuously evolve our controls, infrastructure, and policies as the platform grows.
Security inquiries can be directed to: security@strada.tech
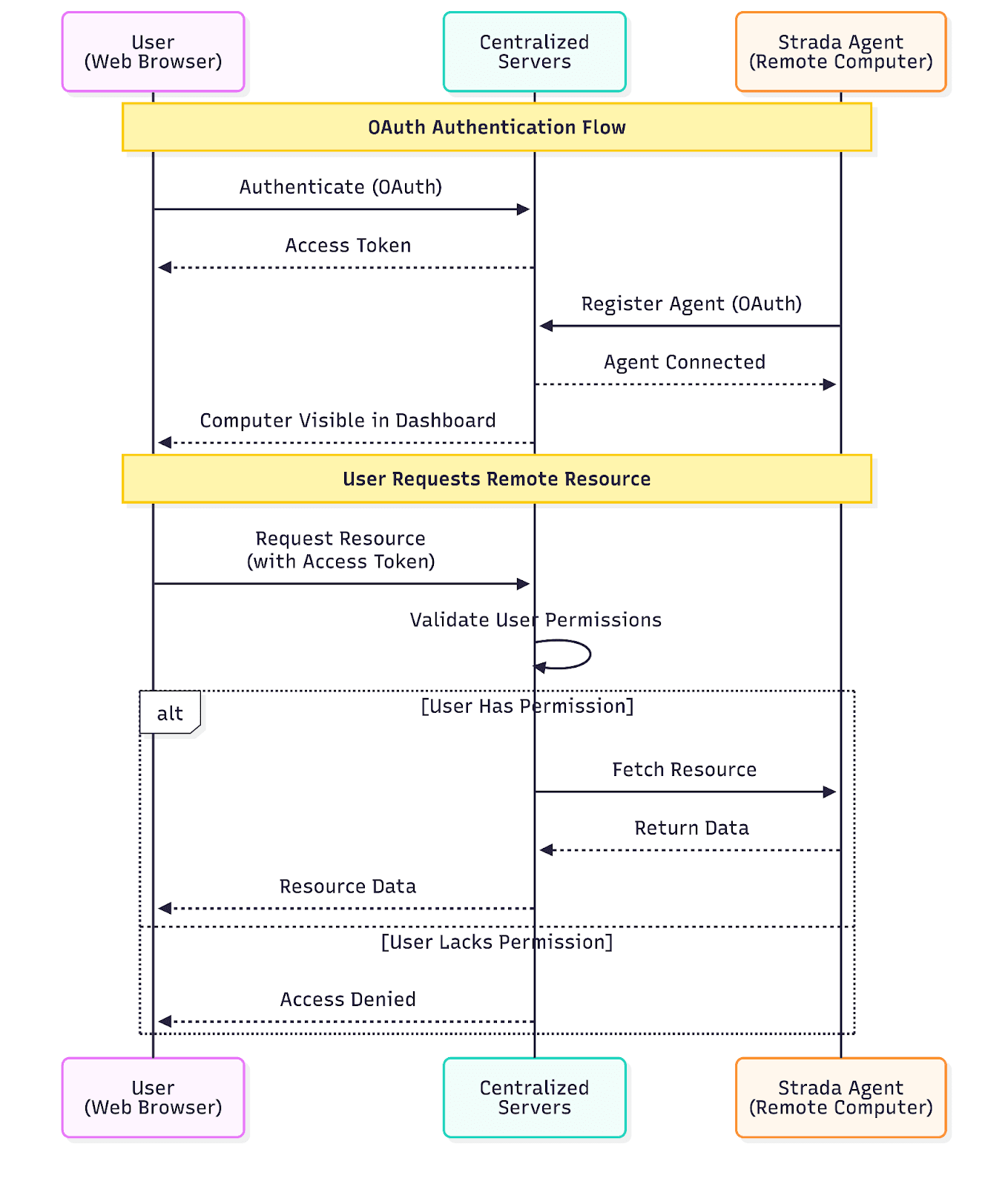
Strada OAuth Remote Access Sequence Diagram
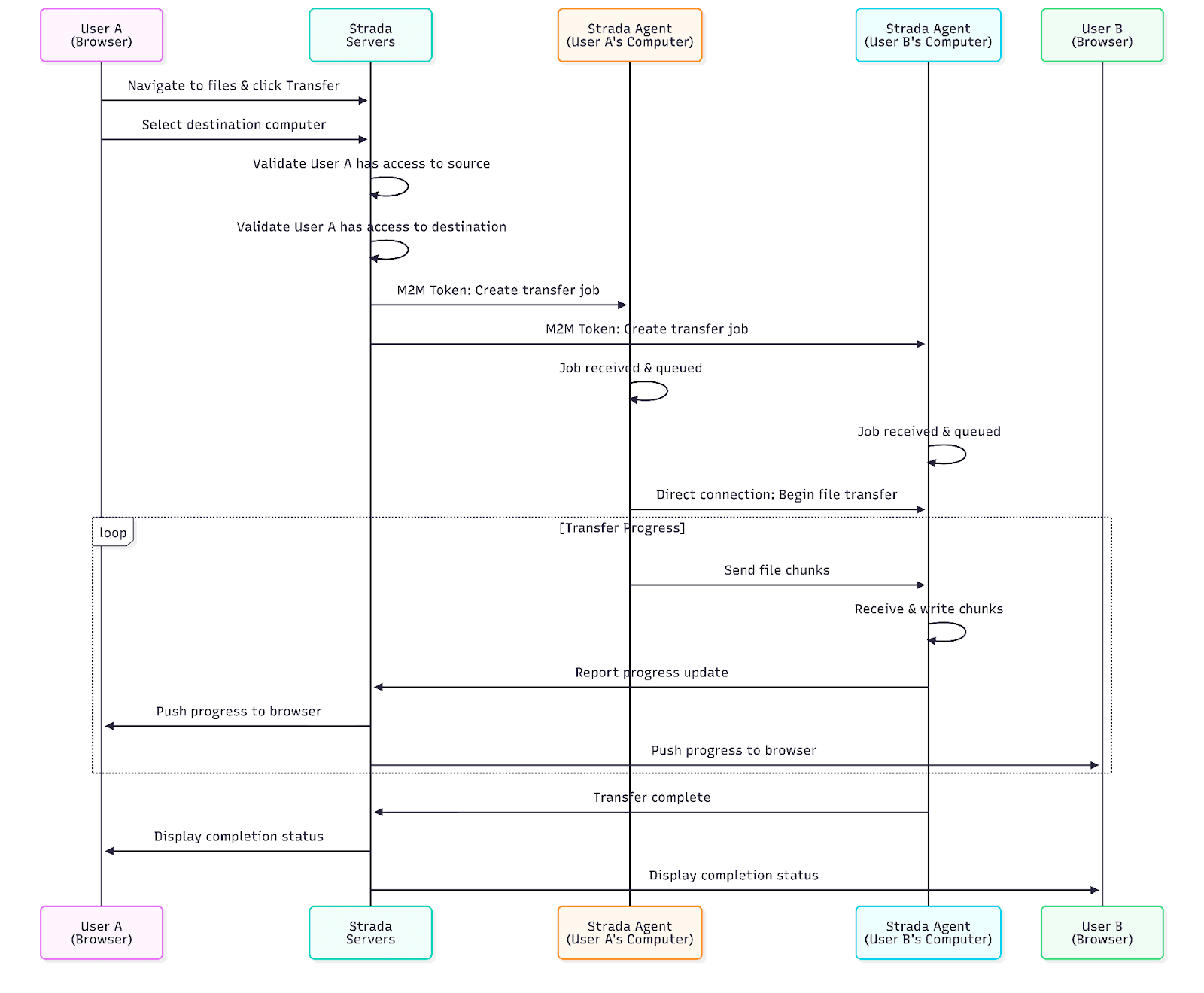
Strada File Transfer Sequence Diagram